Hello,
I'm going to provide you a free guide to perform malware removal and a basic PC tuneup on practically any PC provided that it at least boots to the Windows desktop.
You may be wondering, why a tuneup too? Well, because 99% of the time you encounter a computer with malware related issues, it also needs some form of a tune up as well. In fact, I include a tuneup on all computers that come in with malware related issues.
A Tuneup, to me, entails:
- Removing expired anti-virus, anti-spyware programs
- Removing unrecommended programs
- You have to be pretty delicate on this one, because you don't want to piss off a customer that actually paid for "UniBlue Registry Booster 2013", "Spyware Doctor", or similar unrecommended programs. Ask the customer first before removing a program if you are unsure.
- Removing outdated versions of programs.
- We don't need to update every single program on the customer's computer, just the essential ones if they are present.
- These are the ones I will update for the customer if they were installed. Mozilla FireFox, Google Chrome, Java SE, Adobe Reader, Adobe Flash Player.
- Then, depending on time and necessity:
- 3 stage CheckDisk (chkdsk) and full defrag using Puran Defrag's Boot Defrag features.
- Note: Remember to clear the system restore points first!
- Windows Updates / Service Pack updates
__
Ok that is enough about TuneUp, we'll go into more detail later on.
First, you just received a computer and it has a bunch of malware on it. It is so slow and needs your help!
First thing is first, and if we are allowed to, we want to uninstall any outdated antivirus and antispyware programs. These will just get in our way if they are expired and are spamming "You are not protected!" messages every 10 seconds.
Go ahead and begin uninstalling one and if you are Windows Vista, Windows Seven, or Windows Eight, turn off User Account Control (UAC) as that will slow us down as well. We will turn it back on when we are all finished. We are going to be running many programs pretty soon and we do not need a confirmation box every single time.
If you are currently uninstalling someone's expired antivirus, we will need to reboot the computer soon. UAC also requires that we reboot before the changes to take affect (not so true if on Windows Seven, but Vista always true).
Keep in ind that we will rebooting very soon, before we do, we want to remove unneeded start up items using
Autoruns. Why? Well we do not want every single program the customer has installed trying to run yet again. In fact, we could have run Autoruns from Safe Mode where we could have avoided dealing with the majority of unnecessary startups, the only downside is, you won't be able to uninstall most programs due to them requiring Windows Installer Service.
I do have a little trick for that, starting Windows Installer Service while you are in Safe Mode.
You can save the following as a batch file or enter the commands one at a time from a command prompt window.
REG ADD "HKLM\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\MSIServer" /VE /T REG_SZ /F /D "Service"
net start msiserver
or, if you are in Safe Mode with Networking, use this one instead:
REG ADD "HKLM\SYSTEM\CurrentControlSet\Control\SafeBoot\Network\MSIServer" /VE /T REG_SZ /F /D "Service"
net start msiserver
You should have now at least run Autoruns by now. Removed unnecessary startups. If you did have an expired antivirus to uninstall, and you have turned UAC off, go ahead and reboot now and upon reboot, continue to uninstall unnecessary programs.
If you did NOT have an antivirus to uninstall, turn UAC off but continue to uninstall unnecessary programs. Remember, get permission from the customer. Usually, they won't have a clue as to what you are talking about, but you can at least say that you received permission to uninstall said program(s).
Depending on what type of infection you are dealing should dictate which order of tools you should be running. What if you weren't even able to go into Control Panel to remove programs or to turn off UAC? In these cases, we need to perform some repairs on Windows first and/or stop/delete the most active malware.
RogueKiller is an all around good security application that can allow you to get some breathing room so to speak. It kills off bad processes that may be bogging the computer down and also works as a infection identifier and cleaner.
It also has a "Fix Shortcuts" button which will restore missing desktop / start menu items in case you ran into a Fake.HDD (hard drive) type of virus.
I typically will at least Scan with RogueKiller and then Delete almost everything it finds except for correcting the UAC entires that we just turned off.
They will appear as "ConsentPromptBehaviorAdmin" and "EnableLUA" in the registry tab of the report. You can leave these unchecked and fix everything else by using the "Delete" button. A reboot may be required. Go ahead and reboot if prompted.
Just to recap, we've uninstalled any outdated antivirus programs and unrecommended and/or outdated programs. (Mozilla FireFox, Google Chrome, Java SE, Adobe Reader, Adobe Flash Player). We've also run a Delete with RogueKiller and our machine is coming back to life (maybe not so noticeable yet).
Now is a good time to kill off unnecessary processes. I typically just use the Task Manager although you may prefer a tool like
Process Explorer. Task Manager is enough for what we are doing here, but feel free to use an alternative.
Now would be a good time to make a backup of the registry, just incase something goes bad from this point forward. I use
ERUNT. Once you have successfully backed up the registry, now we can delete all the existing restore points. This will reduce scan times and we really only need 1 reliable restore point which we just created using ERUNT.
Next, let's run a scan of
TDSSKiller . It should be a fairy quick scan. Reboot if threats were found, either way, continue on:
Next, we are going to install
CCleaner Slim. Now run CCleaner Slim and also opt to delete Event Viewer Logs and Flush DNS. This is also a handy tool to use as an alternative "Add Remove Programs / Programs and Features". Removing any remaining unnecessary programs from here if you weren't able to access them normally before. Now go into the Registry tab of CCleaner. Click "Scan for Issues" and then "Fix Selected Issues". CCleaner is the only safe registry optimizer in my book. I've never ever encountered an issue, but just in case we did, we have our ERUNT backup ;)
Next, how about some malware removal?!?!
Download and install, and update
MalwareBytes' Anti-Malware.
Now open the program and go into the "Settings" tab, from there, select the "Scanner Settings" sub-tab.
Change the following options to match the below:
Action for potentially unwanted programs (PUP) : Show in results list and check for removal
Action for potentially unwanted modifications (PUM) : Show in results list and check for removal
Action for peer-to-peer software (P2P) : Show in results list and check for removal
Now go back to the main Scanner tab and choose "Perform Quick Scan" and then click the "Scan" button.
Follow MBAM's prompts, if a reboot is needed, reboot!
__
Once MalwareBytes' Anti-Malware is finished, download and run
HitmanPro.
Remember to opt to delete Potentially unwanted programs as well (it's in the Settings section).
__
At this point, the computer should be running pretty smoothly. Maybe there are some lingering issues which we'll address now.
Now's a pretty good time to download and run
Junkware Removal Tool.
Read the description in the link provided as to what it does. It's basically a maintenance tool but also addresses some browser issues.
Then you can download and run a similar program called
AdwCleaner (Adware Cleaner).
To be thorough, I like running a scan and deleting any leftovers found using
OTL.
__
- If there are not any other issues, start uninstalling / removing the programs you installed / used.
- Create one more registry backup using ERUNT.
- If time allows, do some basic maintence, service pack updates, Windows Update, chkdsk and defrag
- Remove all traces of your tools - Note, you can use OTL CleanUp button for this.
- Turn System Restore back on for the systemdrive only.
- Turn on User Account Control.
The end. Will format this later and correct any errors I may have made.!



 Press F8 upon boot to get to the Windows Advanced Options Menu
Press F8 upon boot to get to the Windows Advanced Options Menu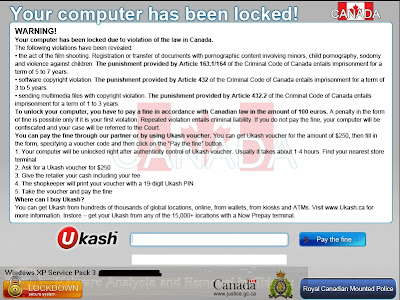







 Results in the screen to the right:
Results in the screen to the right:




